CyberSecurityDay
2025
Jesenná 5, 040 01 Košice
Faculty of Science, UPJŠ
CyberSecurity
Day
2025
Jesenná 5, 040 01 Košice
Faculty of Science, UPJŠ
Spring CyberSecurityDay (Rožňava)
07.04.2025
Stredná odborná škola technická, Hviezdoslavova 5, 048 01 Rožňava
Practical workshops based on real-world experiences in resolving computer security incidents. An opportunity to talk to people who are professionally involved in information and cybersecurity, to meet new people, and compete for interesting prizes.




Agenda
Lecture
Current Security Threats
Monika Rapavá (CSIRT-UPJS)
A basic introductory lecture intended primarily for students and the general public. It introduces the concepts of cybersecurity, types of attacks, security incidents and the legal framework for data protection.
Workshops
Mobile Device Security
Jakub Mohler (CSIRT-UPJS) / Monika Rapavá (CSIRT-UPJS)
The workshop focuses on current threats and vulnerabilities in the field of mobile devices. Participants will be introduced to practical examples of attacks, as well as malware using hardware functions of devices. Security measures, correct permission settings and risks of older versions of operating systems are also discussed. There is also a recommendation for testing tools.
Resolving cyber security incidents
Pavol Sokol (CSIRT-UPJS), Monika Rapavá (CSIRT-UPJS)
A summary of real cyber incidents, their impact and solutions, the perfect workshop to broaden your knowledge in the field of cybersecurity. It focuses on lessons learned from incidents, procedures for resolving them, and recommendations for institutions.
Personal data protection
Simona Rudohradská (Faculty of Law UPJŠ)
During the workshop high school students will learn what personal data is, how it can be recognized in everyday life, and why its protection is one of the fundamental rights of every person. Participants will also learn the basic principles of personal data processing, such as legality, fairness, transparency, data minimization, and the principle of limiting the usage of your personal data. Using specific examples, we will explain how these principles affect situations they may encounter, for example, at school, on social networks, or when using mobile applications. Students will also learn what rights they have as data subjects – for example, the right to access, the right to rectification, erasure or objection to processing. Through practical activities, we will teach them how to exercise these rights and who they can contact in case of a violation of their rights.
Spring CyberSecurityDay
24.05.2025
Practical workshops based on real-world experiences in resolving computer security incidents. An opportunity to talk to people who are professionally involved in information and cybersecurity, to meet new people, and compete for interesting prizes.







Agenda
Lecture
Critical thinking against myths and manipulations
Peter Dubóczi (Faculty of Philosophy UPJŠ)
This lecture will introduce high school students to what disinformation is, why it is so effective today and how to distinguish it from conspiracy theories, hoaxes, and other manipulative phenomena. It will also focus on why we as humans are subject to it and what vulnerabilities in us manipulators exploit. However, we will not stop at describing the problem. The workshop also presents tools and strategies for developing critical thinking, verifying information and safe behavior in the digital environment.
Workshops
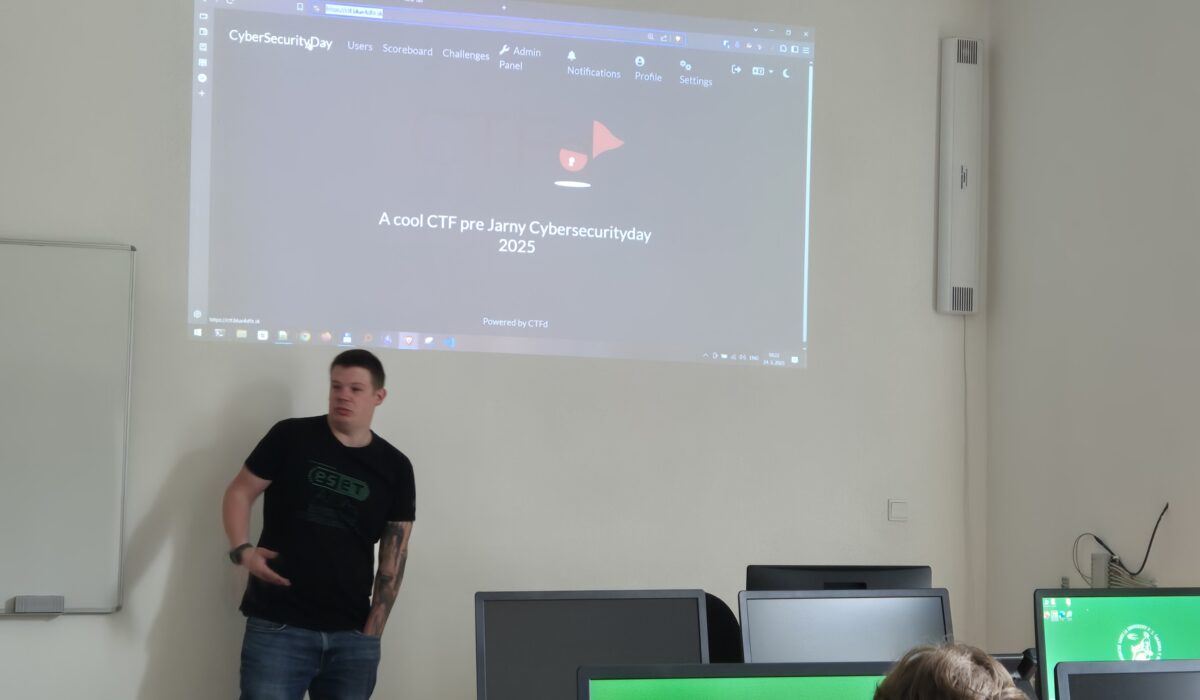
CTF Workshop: Your start in the world of cybersecurity
Miroslav Sidor (ESET)
Level: low
Do you know what connects ethical hackers and various cybersecurity specialists? They all train their skills through CTF (Capture The Flag) challenges that combine training and fun in one place. In this 60-minute workshop, you will learn the basic types of CTF tasks and we will try to solve some of them together. The workshop is practical and suitable even for complete beginners. Na tomto 60-minútovom workshope spoznáš základné typy CTF úloh a niektoré z nich si spoločne vyskúšame. Workshop je praktický a vhodný aj pre úplných začiatočníkov.
Cybersecurity Incident Response 101
Jakub Mohler (CSIRT-UPJS)
Level: low
Imagine turning on your computer at school and instead of a regular screen, you are greeted by a ransom note. Data is encrypted, time is running out, and the entire school system is paralyzed. What now? Holidays! In this workshop, you will learn the basics of handling cybersecurity incidents — from initial response to evaluating and preventing a recurrence of the problem. However, it will not just be about sitting and listening. You will be presented with realistic situations that you will react to, make decisions, and discuss their consequences with other participants. You will gain an overview of what a cyber incident actually is and how to recognize it, what are the basic steps for resolving incidents, why it is important to communicate and document and what we can learn from mistakes (including those of others).
AI in Cybersecurity: Working with Large Language Models
Sophia Petra Krišáková (Faculty of Science UPJŠ)
Level: Intermediate
During this workshop you will learn what large language models (such as ChatGPT) are, what they are used for, and how they actually work. We will showcase these models on practical examples from the field of cyber and information security - that is, how they can help detect threats or protect against attacks. You will have the opportunity to work with several such models, try them out, and compare the ways in which they are the same and how they differ.
Autumn CyberSecurityDay
29.11.2025
Practical workshops based on real-world experiences in resolving computer security incidents. An opportunity to talk to people who are professionally involved in information and cybersecurity, to meet new people, and compete for interesting prizes.







Agenda
Lecture
Behind the Curtains of Cybersecurity
Alexandra Rusňáková (Axenta), Monika Rapavá (CSIRT-UPJS), Sophia Petra Krišáková (Faculty of Science UPJŠ)
This lecture will introduce you to what the work of cybersecurity experts looks like in the real world. You will learn how research into new ways of protecting systems is done, how the security of organizations is verified through audits, and what happens when a cybersecurity incident occurs. The lecturers will show what problems they encounter on the daily, how they solve them, and why their work is important for the security of each of us. If you are interested in how your enthusiasm for IT can be turned into an interesting and dutiful profession, this lecture is for you.
Workshops
A Practical Guide to Phishing
Michal Copko (SPŠE Košice)
Level: low
Have you ever wondered how attackers, whose main tool is phishing, think? Do you want to know what tools they use to create phishing sites? Come to a workshop where you will learn the main features of social engineering, try you hand at writing a phishing email and create a page that looks strikingly similar to those used by large (and small) web services. The workshop will use Kali Linux and its tools, along with a little help from a language model.
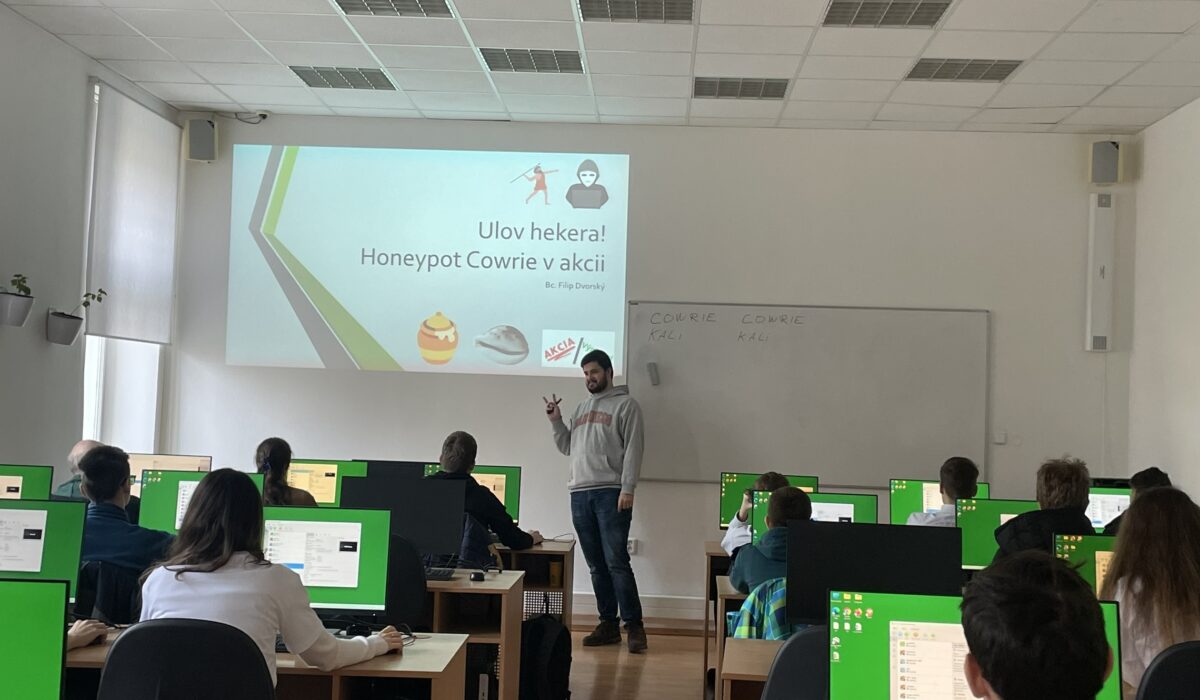
Catch a Hacker! Honeypot Cowrie in Action
Filip Dvorský (CSIRT-UPJS)
Level: Intermediate
The workshop will introduce participants to the world of cybersecurity and show them how to use a honeypot to monitor attackers' behavior. Participants will try working with the Cowrie honeypot, see typical attacks and learn to read system intrusion logs. They will learn to understand how hackers try to gain access and how these attempts can be safely analyzed. The workshop is intended for high school students interested in cybersecurity.
Artificial Intelligence Security: Risks and Defense in Practice
Sophia Petra Krišáková (Faculty of Science UPJŠ)
Level: Intermediate
During this workshop participants will try out various vulnerabilities in artificial intelligence in practice and understand why its security is crucial. We will demonstrate simple attacks on AI models and explain how they can lead to unexpected errors or incorrect decisions. Together, we will look for ways to minimize these risks and increase the reliability of systems. The workshop is interactive and suitable for high school students interested in technology, programming, and cybersecurity.
Critical Thinking in Practice: How to Avoid Getting Caught
Peter Dubóczi (Faculty of Philosophy)
Level: low
Are you curious about why misinformation, hoaxes, and conspiracy theories spread so quickly — and, most importantly, how to avoid falling for them? Come to an interactive workshop focused on critical thinking and media literacy, which will explain what cognitive vulnerabilities and mechanisms of manipulation attack our decision-making. You will master simple frameworks and key questions that help to quickly distinguish fact from manipulation. The workshop is designed for high school students and does not require any special knowledge, except for curiosity or a willingness to engage in discussion.






